2026 February Meeting Notes: Effective Strategies for Comprehensive Risk Management & Panel Discussion (Black Leaders in Cybersecurity)
Effective Strategies for Comprehensive Risk Management + Panel Discussion (Black Leaders Making Strides in Cybersecurity)
In celebration of Black History Month, the ISC2 Toronto Chapter hosted an engaging evening of learning, discussion, and networking featuring cybersecurity leaders who are shaping the future of the industry. The event highlighted the contributions of Black professionals in cybersecurity and brought together practitioners, students, and industry leaders to discuss modern security challenges and leadership in the field.
The evening featured a keynote presentation by Dele Saliu, Head of IT Governance Risk and Compliance Centre of Excellence at Aviva Canada, followed by an insightful panel discussion with cybersecurity leaders on innovation, leadership, and the evolving threat landscape.
Keynote Presentation - Effective Strategies for Comprehensive Risk Management
Dele Saliu opened the evening by discussing the importance of comprehensive risk management in modern technology environments. With over 20 years of experience across compliance, application security, cloud engineering, and governance, he shared practical insights drawn from his work in financial institutions and insurance organizations.
He emphasized that risk management is not limited to security teams — everyone in an organization plays a role in identifying and managing risks.
Key Themes from the Presentation
1. Understanding Risk in Technology
Risk exists in every technological interaction, from digital payments to cloud infrastructure. Organizations must protect critical assets by ensuring the confidentiality, integrity, and availability (CIA triad) of their systems.
Risk management should be:
- Evidence-driven and aligned with business objectives
- Integrated with organizational operations
- Adaptable to changing business environments
2. Importance of Comprehensive Risk Management
Organizations today face increasing cybersecurity and operational risks due to the expanding digital landscape.
To manage these risks effectively, organizations should adopt recognized frameworks such as NIST Risk Management Framework (RMF) and ISO 27001.
These frameworks provide structured approaches to managing risk while ensuring compliance with regulatory requirements.
Effective risk management helps organizations achieve:
- Business continuity and resilience
- Stakeholder confidence and regulatory compliance
- Proactive threat mitigation
3. The NIST Risk Management Framework (RMF)
Saliu explained the seven-step lifecycle of the NIST RMF, which forms a continuous cycle of risk management. For further reading, check the official NIST RMF guidelines.
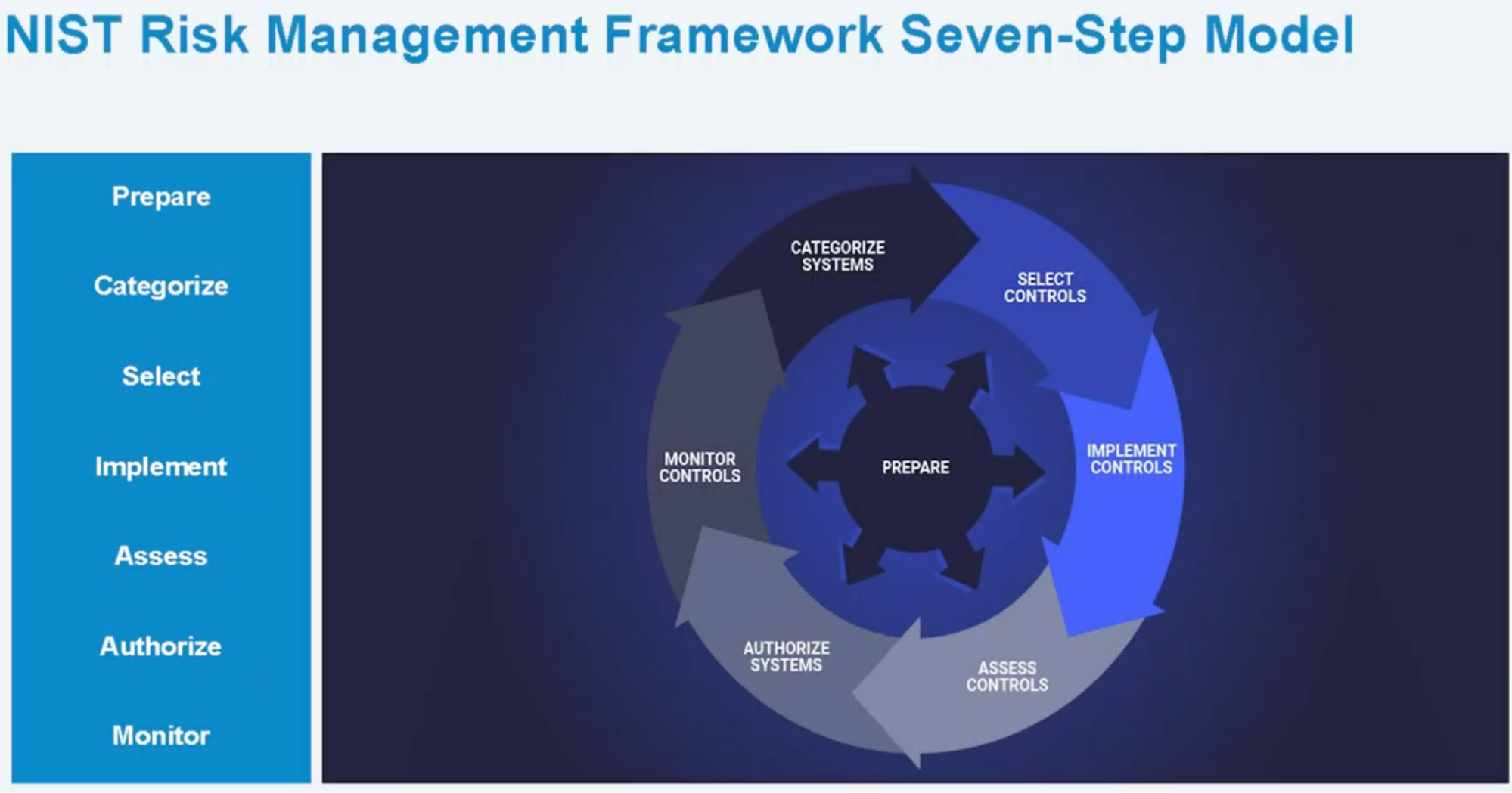
The key steps include:
- Prepare – Establish governance structures and define roles and responsibilities.
- Categorize – Conduct business impact analysis and classify systems based on risk levels.
- Select – Choose appropriate security controls from standards such as NIST SP 800-53.
- Implement – Operationalize security controls and integrate them into systems.
- Assess – Test controls to identify gaps or weaknesses.
- Authorize – Approve systems for operation based on risk posture.
- Monitor – Continuously track risks, vulnerabilities, and control effectiveness.
Saliu highlighted that risk management is cyclical, not linear, requiring ongoing monitoring and adaptation.
Challenges in Risk Management
Saliu also shared some of the common challenges that organizations faced such as:
- Resource constraints
- Stakeholder alignment
- Legacy systems and technical debt
- Quantifying risk impact
Key Takeaways:
- NIST RMF provides a structured, proven methodology for comprehensive risk management
- Success requires integration across all seven steps as a continuous cycle
- Governance, communication, and stakeholder alignment are critical enablers
- Practical implementation must balance security, operations, and business objectives
- Data-driven monitoring and continuous improvement maintain effectiveness
Panel Discussion - Black Leaders Making Strides in Cybersecurity
The keynote was followed by a dynamic panel moderated by Vivian (ISC2 Toronto Chapter Secretary), featuring leaders from across the cybersecurity industry.
Panelists:
- Ireen Birungi – Chief Information Security Officer (CISO), at Interac Corp.
- Akinniyi Ojo – Director Cybersecurity Operations, Dayforce
- Fola Adegoke – GRC Lead, Career Coach, Instructor at Winfinite Consult
- Emmanuel Onuoha – Founder, AI Guardium
The panel explored leadership journeys, emerging technologies, and the skills needed to succeed in cybersecurity.
Panel Highlights
1. The Role of Cybersecurity Leaders Panelists discussed how cybersecurity leaders today must balance security risks, business priorities, regulatory compliance, and organizational culture. Panelists also noted that cybersecurity leaders must protect organizational assets while maintaining trust with customers, regulators, and stakeholders, often navigating tension between enabling business operations and enforcing security controls.
2. Predictive Security and Threat Intelligence A central theme of the panel discussion was the industry’s transition from reactive security to predictive security. Traditionally, cybersecurity teams focused on responding to threats after they occurred. However, with today’s rapidly evolving threat landscape, organizations must shift toward anticipating attacks before they cause damage.
Key elements of predictive security include:
- Threat Intelligence – Gathering and analyzing information about emerging threats, attacker tactics, and global cyber trends.
- Behavioral Analytics – Monitoring user and system behavior to detect anomalies that may signal malicious activity.
- Automation and AI-Driven Detection – Leveraging machine learning and automated tools to analyze large volumes of security data and identify threats faster than traditional manual approaches.
3. AI Governance and Emerging Risks AI emerged as one of the most prominent topics during the panel discussion, reflecting its rapidly growing influence across industries. While AI offers powerful capabilities to improve efficiency, automation, and decision-making, panelists emphasized that organizations must also address the new risks and governance challenges that accompany its adoption.
Panelists highlighted several challenges organizations face when adopting AI:
- Shadow AI Usage – Employees using generative AI tools without formal approval or oversight, potentially exposing sensitive data.
- Lack of Governance Policies – Many organizations are adopting AI faster than they can establish proper governance, compliance, and risk management frameworks.
- Managing AI Models and Large Language Models (LLMs) – Ensuring proper oversight of model training, data usage, model behavior, and lifecycle management.
- Security Risks from Autonomous or Agentic AI Systems – AI systems that can perform tasks independently introduce new risks related to access control, decision transparency, and accountability.
Rather than blocking AI tools outright, panelists suggested organizations should implement structured governance frameworks for safe adoption.
4. Skills Needed for Future Cybersecurity Leaders Panelists emphasized that technical expertise alone is not enough to succeed in cybersecurity leadership roles.
Important skills include:
- Risk Translation - Cybersecurity professionals must translate technical risks into business language executives understand.
- Influence and Communication - Security leaders must persuade stakeholders without direct authority.
- Business Understanding - Cybersecurity decisions must consider financial impact and organizational priorities.
- Human-Centric Leadership - Building strong teams and trust within the organization is critical.
5. Advice for Aspiring Cybersecurity Leaders Panelists offered practical advice for professionals seeking leadership roles:
- Obtain relevant certifications and foundational knowledge
- Develop business communication skills
- Understand industry trends and emerging technologies
- Build strong professional networks
- Volunteer for challenging projects and cross-team initiatives